Welcome to Oxzep7
Welcome to Oxzep7, a forward-focused platform founded by Kelros Rothwynd and rooted in Lincoln, Nebraska. At Oxzep7, our mission is to provide concise, comprehensive insights into core technological concepts and their evolving relevance in today’s digital world. Whether you’re deciphering the mechanics of artificial intelligence or unraveling quantum computing’s implications for cybersecurity, our content blends clarity with depth to equip you with understanding that withstands the pace of unprecedented innovation.
AI Values Exchange
Welcome to the AI Values Exchange — an intentional space within Oxzep7 where thoughtful ideas converge, and meaningful conversation around technology, ethics, and discovery is encouraged. This forum isn’t just about information; it’s about interpretation, collaboration, and curiosity. Whether you’re discussing the potential of AI, probing the implications of quantum computing threats, or seeking insight on critical devices and systems — we ask that you participate with care, clarity, and consideration.
Our Latest Blogs

Smartphone Issues Fix
Is your smartphone driving you nuts? I get it. We’ve all been there. The slow loading, the battery that dies in a blink, or those inexplicable glitches…

National Security Concerns Surrounding Quantum Advancements
Quantum breakthroughs are no longer confined to research labs—they’re rapidly reshaping global power structures. If you’re searching for clarity on quantum technology national security, you’re likely trying to understand how emerging quantum capabilities could disrupt encryption, intelligence systems, defense infrastructure, and geopolitical stability. This article directly addresses that concern. We

Risks to Blockchain Technology in a Quantum Future
If you’re searching for clear, practical insights into today’s most important tech shifts—from AI and machine learning to emerging quantum threats—you’re in the right place. The pace of innovation is accelerating, but so are the risks, misconceptions, and technical blind spots that come with it. This article is designed to

Quantum Supremacy and Its Implications for Cybersecurity
A fundamental shift in computing is closer than most organizations realize—and its consequences for digital security are profound. As quantum machines advance, the quantum supremacy cybersecurity impact moves from theory to urgent reality. Today’s encryption systems, which safeguard online banking, corporate data, and state secrets, rely on mathematical problems that

Post-Quantum Cryptography: Preparing for the Next Security Era
Quantum computing is no longer a distant theory—it’s advancing quickly enough to pose real questions about the security systems we rely on today. If you’re searching for clear, reliable insight into how quantum threats could impact encryption and what post-quantum cryptography standards mean for businesses, developers, and everyday users, you’re

How Quantum Computers Could Break Modern Encryption
Quantum computing is no longer a distant theory—it’s advancing rapidly, and with it comes a new wave of security concerns. If you’re here, you’re likely trying to understand how emerging technologies could disrupt today’s encryption standards and what that means for your data, devices, and digital privacy. This article directly
Create Your Super Reality
Our Catagories
Event Trigger Tool
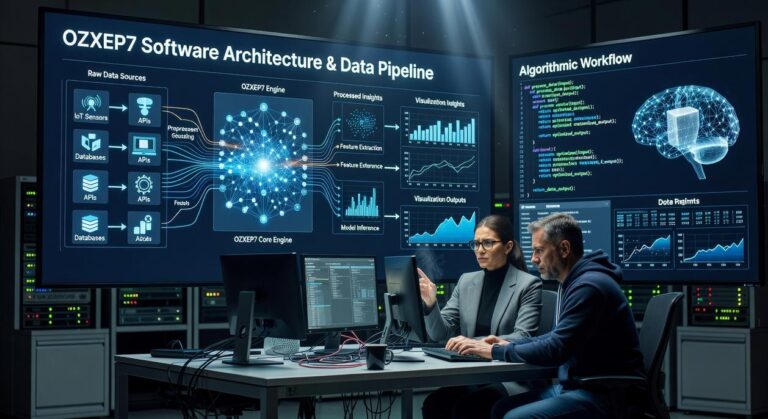
Welcome to the Event Trigger Tool from Oxzep7—your intelligent companion in understanding, managing, and responding to critical technical events. Designed for readiness and built for clarity, the Event Trigger Tool is a precision utility aimed at professionals, researchers, and security-conscious explorers navigating today’s layered tech environment.
News & Articles

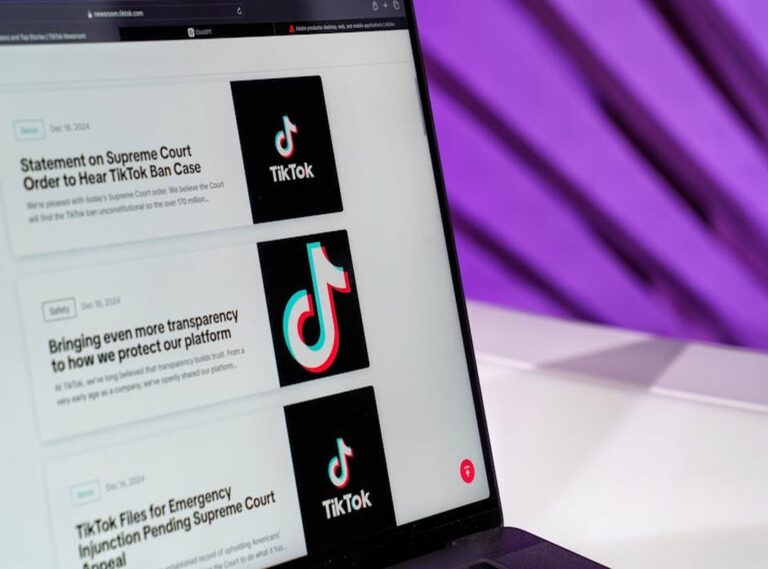
Quantum Cyber Threats
Phishing? It’s old news. We’re facing a new beast now. Traditional cybersecurity methods? They’re falling behind.

Building Your First Machine Learning Model Step by Step
If you’re searching for a clear, practical machine learning model tutorial, you likely want more
Cloud Computing Basics
The term “cloud” gets thrown around so much it feels like everyone’s talking about it, but ask them what it really means? Blank stares. It’s frustrating.